The Movement Pivoting and Persistence course from Joe Helle will be retired on November 15, 2023. This course will no longer be available… | Instagram

Heath Adams on LinkedIn: Movement, Pivoting and Persistence for Pentesters and Ethical Hackers | 105 comments

Active Directory Lab Setup - (Mayor's Movement, Pivoting & Persistence Course Walkthrough) | Oste's Blog

TCM Security on X: "Take your penetration testing skills to the next level. Get Movement, Pivoting, and Persistence from Joe Helle right now for only $1.00 USD! Use the coupon code: OK_FINE_I_WILL_TOO

TCM Security on X: "Movement, Pivoting, and Persistence for Pentesters and Ethical Hackers is the next step in YOUR penetration testing and ethical hacking journey. https://t.co/5Ver3j2SBd #pentest #pentesters #ethicalhacking #penetrationtest https://t ...
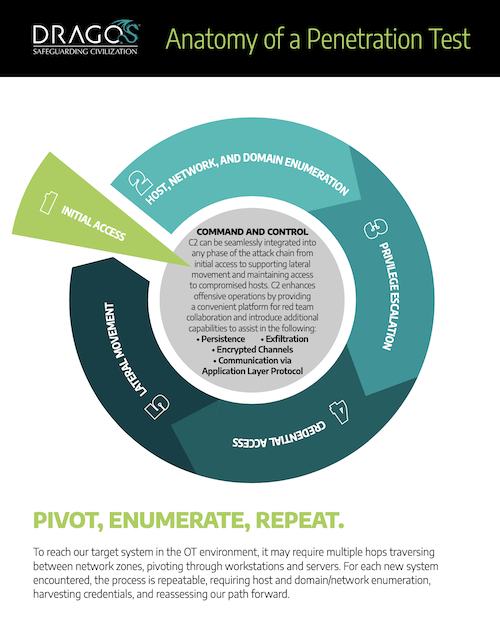
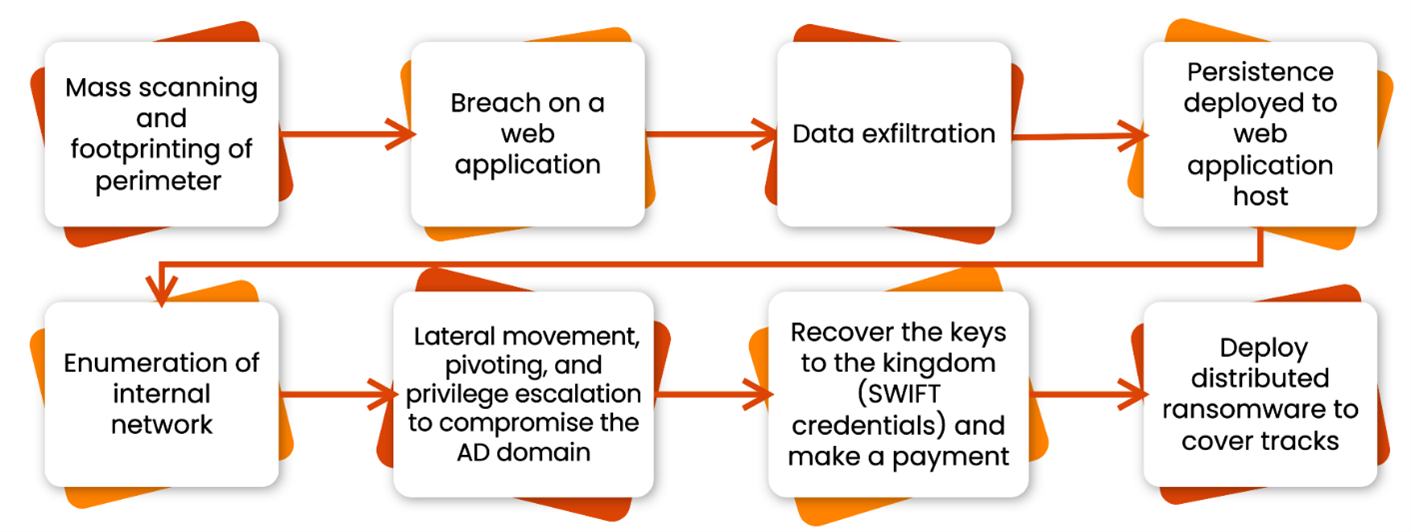
14.5 Understanding Pivoting and Lateral Movement - Security Penetration Testing The Art of Hacking Series LiveLessons [Video]

Active Directory Lab Setup - (Mayor's Movement, Pivoting & Persistence Course Walkthrough) | Oste's Blog

Sneak Peek III (Final) - Workstation Dominance Part 6 - Dumping Firefox Credentials with Metasploit - YouTube

Today is the FINAL day to grab the Movement, Pivoting, & Persistence Course for $29.99 before it's gone forever! If you own the course… | Instagram
PDF) 'Fixation' and 'the pivot': Balancing persistence with flexibility in design and entrepreneurship